I joined Report URI, the real-time security reporting tool, a year ago. In fact, my first code change was June 27, 2017. Since then I've added 709,402 more lines. And deleted 1,981,599 lines.

Report URI was founded by Scott Helme some time in 2015, we've met briefly the same year at DEF CON in Las Vegas, chatting about things like weather and XSS. Since then I've been talking about the reporting service in many of my talks. One of them was called XSS PHP CSP ETC OMG WTF BBQ (in Czech), Scott liked the title for some reason and even started using a similar one. And that means something!
Photo: Scott Helme
After building various payment systems for Skype, changing password hashing and more in local daily deal site called Slevomat (later acquired by Secret Escapes), working as a security engineer for Apiary (now Oracle), I missed building things that matter. I often break things (I mean research things) and teach people how to build stuff securely and was looking for a project to get my hands dirty again.
So one day in late spring 2017 Scott hits me up: Hey wanna join? My immediate response was, like, yeah. So I did. End of story. Actually, no, that's where the fun began.
Report URI is a real-time web security reporting tool. That means when a visitor loads your site and their browser triggers a security violation, that very same browser will send a report with details what happened and where. Your visitors are sending you reports what happened with your site in their browsers. How cool is that?
There are now roughly 5 browser features (and counting) that can trigger violation reports. The browser might tell you, if instructed, when something goes wrong, for example:
- This page wanted to load a script which I'm not supposed to
- I've loaded this page over HTTPS but it has an image that's loaded over HTTP (by just issuing
Content-Security-Policy-Report-Only: default-src https:; report-uri https://report-uri.com/…HTTP header you can detect mixed content after you've migrated your site to HTTPS) - Or even this URL has triggered my Cross-Site Scripting auditor
- And much more…
You can build the report aggregator yourself or just use a third-party reporting service like Report URI. I tried building such tool for myself before using Report URI but even on a low-traffic site like mine, the number of reports was just too high to read. And we're talking 10 reports per day or so. Report URI offers graphs and filters and gives you an insight of what happened, so you can fix it. Instead of building the same thing I started using and talking about Scott's service. All of this some 2 years before joining.
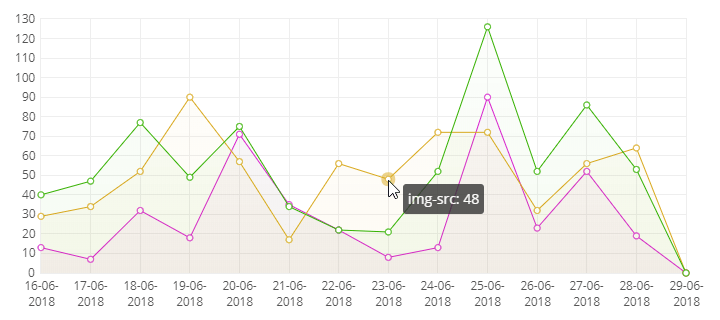
Content Security Policy report graphs
We've launched Report URI v2 on November 1, 2017 and the announcement started with a big news: Troy Hunt has joined Report URI! Troy is a Microsoft MVP (Most Valuable Professional) and Regional Director (it's a Microsoft program for independent experts, not a job title, see what that means), Pluralsight author and runs Have I Been Pwned? – the service you can (and should) use to monitor data breaches for your email addresses, domains, and passwords. Also a frequent topic of my talks and articles.
Since I joined Report URI a year ago, we've introduced quite a list of features already:
- Usage-based pricing to support the growth (announcement)
- Team support, 2FA
- The CSP Wizard to help with configuring your Content Security Policy by allowing or blocking hosts simply in the UI (more about it here)
- Smaller things like better graphs where you can hide series you don't want to see at the moment
- Wildcard hostname filters
- Report URI JS for reporting from hosted platforms like GitHub Pages and Ghost Pro
We've also change the infrastructure a bit to handle the increasing load, started using Cloudflare Workers to speed up the service. We have over 40 servers in the public fleet and then some private instances for enterprise customers too. At peaks, we process over 15k requests per second. The service has seen more than 60 billion reports totally. More numbers in Report URI: A week in numbers.
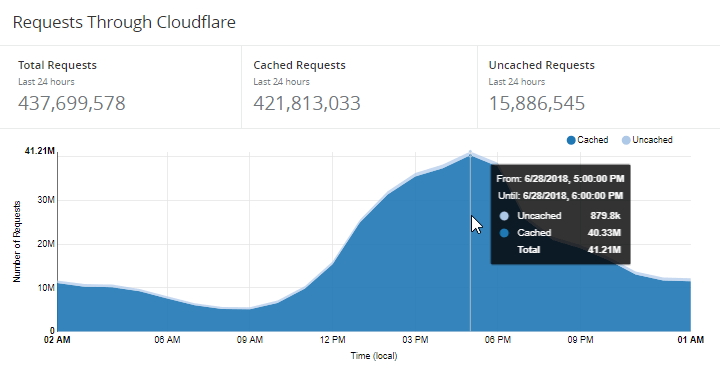
Total requests for last 24 hours: 437.67M; 41.21M in peak hour
The service (and Content Security Policy reporting) is already used by quite a few sites, like a Dutch bank (“Not just the marketing team is seeing their campaigns working, but Security is getting more value.” – Jesse Houwing), and others plan to start using it soon, like for example the developers of EVE Online, the massively multiplayer online role-playing game (“And all of it made a lot easier by using @reporturi!” – Stefán Jökull Sigurðarson).
Oh, and just by the way, Report URI won as the “Best Emerging Technology” at the SC Awards Europe 2018. I still can't believe this one! Read Scott's report and Troy's blog, both were there in person, SC Magazine UK has published a little write-up, too. To us! 🥂
Most of the feature announcements above are linked from Scott's blog because he's doing good job covering the features, while I'm just deleting code, ha ha. Oh, and those 2M deleted lines? Majority of them were deleted in this change:

Removing 1.4 million lines of code 3 weeks after joining the company, what can go wrong…
That was Microsoft Azure SDK being removed, we needed just the Azure Storage SDK, not the full one.
Yeah, working on Report URI is fun.
